Wireshark Tutorial: Analyze Network Traffic Like a Pro
Wireshark is one of the most powerful and widely used network protocol analyzers. It allows you to capture and examine network traffic in real time, making it an essential tool for network troubleshooting, cybersecurity analysis, and learning how data flows across networks.
What is Wireshark?
Wireshark is a free and open-source tool used to monitor and analyze network packets. It helps security professionals, network administrators, and students understand how communication happens between devices on a network.
With Wireshark, you can inspect packets in detail, detect suspicious activity, and troubleshoot network issues efficiently.
Wireshark Welcome Screen:
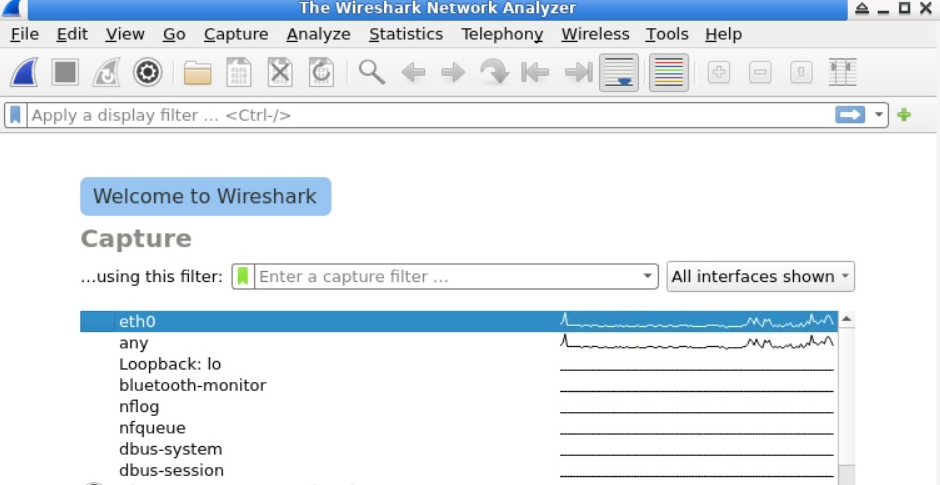
Wireshark Welcome Screen Overview
After launching Wireshark, you will see the welcome screen displaying available network interfaces for capturing traffic.
Key Options Available:
- Select a network interface to start capturing packets instantly
- Open previously saved capture files
- Apply capture filters before starting
Main Interface Elements of Wireshark
Menu Bar
Provides options to save captures, export files, and configure settings.
Toolbar
Quick access to start/stop capture and save data.
Display Filter Bar
Filter packets using IP address, port, or protocol.
Interface List
Shows all available network interfaces such as Wi-Fi or Ethernet.
How to Start Capturing Packets
Select a network interface from the welcome screen. Wireshark will immediately begin capturing traffic.
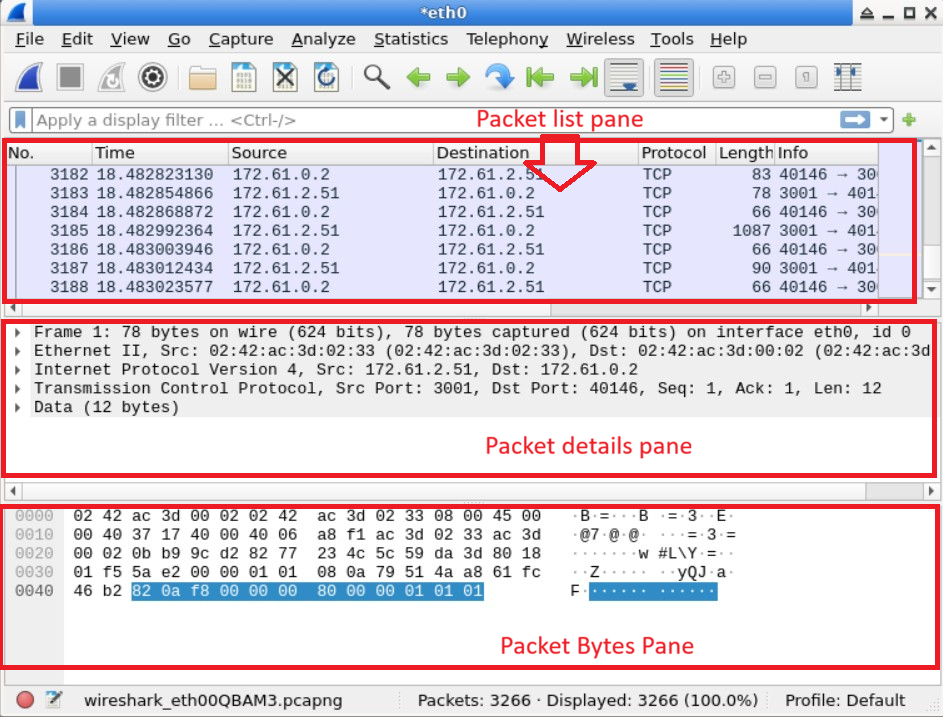
Starting Packet Capture:
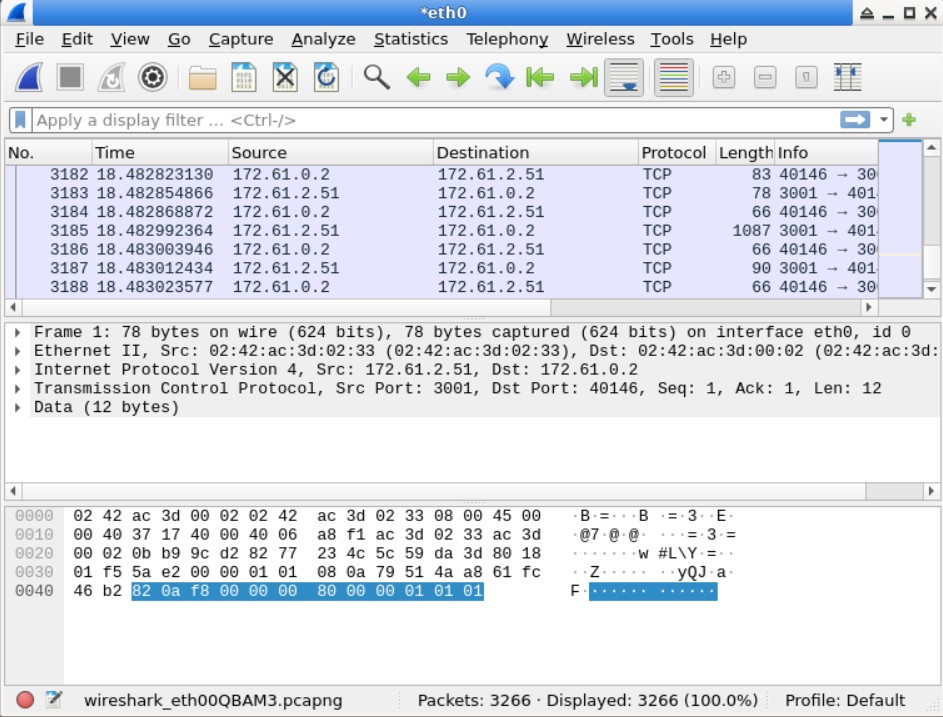
Wireshark Capture Interface Explained
1. Packet List Pane (Top)
- Packet Number
- Time captured
- Source & Destination IP
- Protocol
- Packet length
- Info summary
2. Packet Details Pane (Middle)
Shows detailed breakdown of selected packet in hierarchical format.
3. Packet Bytes Pane (Bottom)
Displays raw data in hexadecimal and ASCII format.
Wireshark Interface:
Generating Network Traffic for Analysis
To analyze packets in Wireshark, you first need to generate some network traffic. A simple way to do this is by using the ping command, which sends ICMP echo request packets to a target server.
Open a terminal and run the following command to send packets to Google servers:
ping google.com
This command generates continuous ICMP requests and responses, which can be captured and analyzed in Wireshark.
Ping Requests to Google:

The screenshot above shows ICMP echo requests being sent to Google. Meanwhile, Wireshark captures these packets in real time, as shown below.
Captured Packets in Wireshark:
 ---
---
Stopping Packet Capture in Wireshark
Once you have captured enough data, you can stop the packet capture process easily.
To stop capturing packets, click on the red square button located in the toolbar at the top of the Wireshark interface.
Stop Capture Button:
 ---
---
Filtering Packets in Wireshark
When capturing network traffic, Wireshark collects a large amount of data. To analyze specific packets, you can use filters to narrow down the results.
Filters allow you to display only the packets that match certain criteria, such as protocol type, IP address, or port number.
Example: Filtering ICMP Packets
To display only ICMP packets (used by the ping command), enter the following filter in the display filter bar:
icmp
After applying this filter, Wireshark will show only ICMP request and reply packets.
Filtered ICMP Packets:
 ---
---
Understanding Filtered Packet Data
After applying the ICMP filter, you will notice two types of packets:
- ICMP Request: Sent from your system to the target server
- ICMP Reply: Response received from the server
When you select a packet, you can analyze it in detail using different panes in Wireshark:
- Packet Details Pane: Shows structured information about the selected packet
- Packet Bytes Pane: Displays raw packet data in hexadecimal and ASCII format
These features allow you to deeply inspect how data is transmitted across the network.
Why Wireshark is Important for Cybersecurity
Wireshark plays a crucial role in modern cybersecurity by allowing analysts to monitor and inspect network traffic in real time. It helps in detecting suspicious activity such as unusual data transfers, unknown connections, or potential intrusion attempts.
Security professionals use Wireshark to analyze different types of cyber attacks, including packet sniffing, man-in-the-middle attacks, and network-based exploits. By examining packet-level data, they can identify how an attack is performed and take appropriate measures to prevent it.
In addition to security analysis, Wireshark is widely used for troubleshooting network issues. It helps identify problems such as slow connections, packet loss, or misconfigured devices by providing detailed insights into how data is being transmitted across the network.
Overall, Wireshark is an essential tool for students, ethical hackers, and network administrators who want to understand network behavior, strengthen security, and build practical cybersecurity skills.
Frequently Asked Questions (FAQs)
Is Wireshark legal to use?
Yes, Wireshark is legal when used for ethical purposes such as network troubleshooting and cybersecurity learning. However, capturing data without permission may violate laws.
Can Wireshark capture passwords?
Wireshark can capture unencrypted data, including passwords sent over insecure protocols. This is why secure protocols like HTTPS are important.
Is Wireshark good for beginners?
Yes, Wireshark is beginner-friendly with practice. It helps users understand how networks work and how data flows between devices.
What is packet sniffing?
Packet sniffing is the process of capturing and analyzing network packets. Wireshark is one of the most popular tools used for this purpose.